
AI Powered DSPM for Data Security and Compliance
Get Visibility and Control over Your Data BreezyAI Discover, classify, and protect sensitive data across your SaaS collaboration tools effortlessly
Human Risk Management & Advanced Email Security
Protect email and collaboration tools with Mimecast. Manage human risk and stay ahead of cyber threats with advanced security solutions.

Hydden
End identity drudgery. Discover every identity, observe behavior in real-time, & confidently act with evidence-backed control.

Protect your people, codebases, and AI-assistants from software supply chain threats
The world's first AI-powered Software Supply Chain Firewall secures every package installation in real-time, automatically blocking malicious and vulnerable dependencies before installation. Stop supply chain attacks at their source while maintaining development velocity.

Secure your dependencies. Ship with confidence.
Socket is a developer-first security platform that protects your code from both vulnerable and malicious dependencies.

Sonatype
Sonatype provides intelligence & automated governance to help you build faster & safer with open source and AI. From the creators of Nexus Repository.
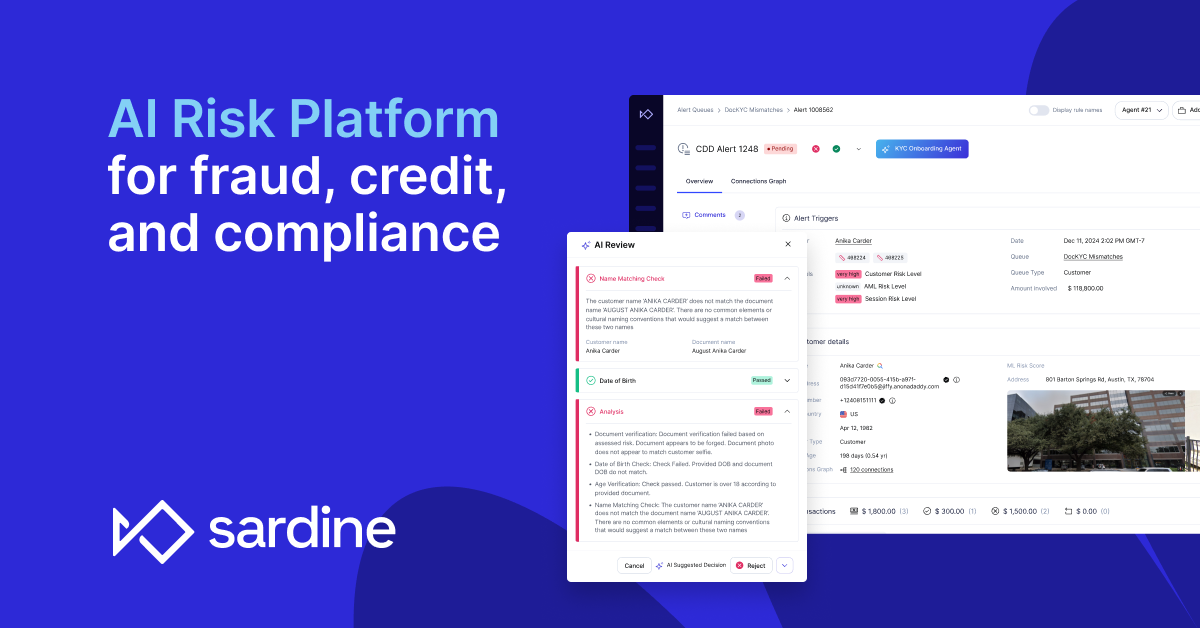
The AI risk platform for fraud, credit, and compliance
Sardine’s AI platform is at the core of enterprise risk and fraud workflows, allowing them to consolidate vendors and improve operational efficiency. Hundreds of enterprises in over 70 countries trust Sardine to stop fraud in real-time, streamline BSA/AML compliance, and unify data across risk teams.

Faster detection. Faster search. Faster resolution.
Rapidly shut down threats with real-time detection, blazing-fast search, and reduced logging costs.